Data Security Compliance: A Cheat Sheet for IT

Whether you work for an organization controlled by compliance standards or you are an independent IT looking to build your enterprise business, industry regulations regarding data security, also known as information security, can sometimes cause a real headache.
Keep reading for a single set of guidelines to follow that can be applied to all industry regulations.
WHY DATA SECURITY REGULATIONS EXIST
Industry-mandated data security requirements are there for a good reason. Social security numbers, credit card numbers, birth dates, and more are all extremely valuable on the black market. Where there is personal data, there are hackers trying to get at it. According to the Identity Theft Resource Center (ITRC), “the number of 2021 data compromises is 23 percent over the previous all-time high.”
There are horror stories about data being stolen by third-party data recovery companies or, worse yet, sold to the highest bidder. This is why it’s incredibly important to have a pre-vetted data recovery company.
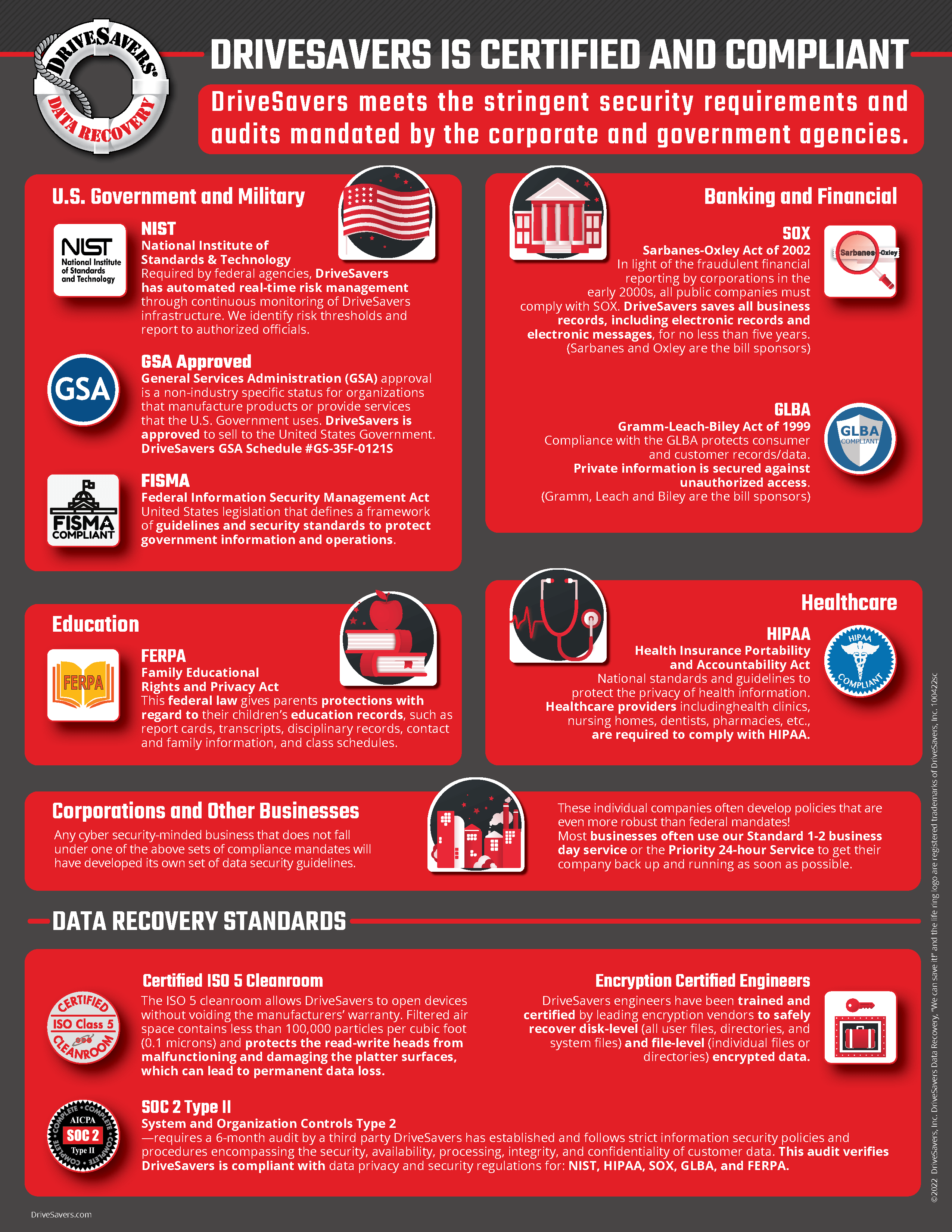
DriveSavers undergoes an annual SOC 2 Type II audit of its internal data hosting and processing controls to guarantee that our data recovery services uphold the stringent data security and privacy protocols mandated by the corporate clients and government agencies we serve. The SOC 2 Type II certification covers all the protocols.
Industry Terms IT Needs to Know
Vocabulary and Compliance Standards
Each of these industries follows a different set of rules with a different set of vocabulary. You should be familiar with the terms that are used in the industries you plan to be working with.
Corporations and Other Businesses
Any cybersecurity-minded business that does not fall under one of the above sets of compliance mandates will have developed its own set of data security guidelines. In fact, these individual companies often develop policies that are even more robust than federal mandates!
Since these companies have developed their own sets of rules and are not following any industry-wide mandate, they often have their own vocabulary as well. It’s important to learn the terms used by any business you provide IT service to, and important to familiarize yourself with their company information security and cybersecurity requirements.
Banking and Financial
As described in section 4(k) of the Bank Holding Company Act, any business that is “significantly engaged” in “financial activities” must comply with GLBA. If a business falls into this category and is also publicly traded, that organization will also need to comply with SOX.
- Non-bank mortgage lenders
- Real estate appraisers
- Loan brokers
- Some financial or investment advisers
- Debt collectors
- Tax return preparers
- Banks
- Real estate settlement service providers
- Any other business that is “significantly engaged” in “financial activities”
Terms you need to know:
- GLBA: Gramm-Leach-Bliley Act
- SOX: Sarbanes–Oxley Act of 2002
- NPI: Nonpublic personal information
Healthcare
Any organizations working in the healthcare space need to comply with HIPAA regulations.
- Health plans
- Health care clearinghouses
- Health care providers
- Business associates of any of the above (including YOU!)
Terms you need to know:
- HIPAA: Health Insurance Portability and Accountability Act of 1996
- ePHI: Electronic protected health information
Education
Any educational institution that receives federal funding of any kind must adhere to FERPA.
- Public elementary schools and high schools
- Private or charter elementary schools and high schools that receive any federal funding
- State colleges and universities
- Private colleges or universities that receive any federal funding
- Any other educational organization that receives any federal funding
Terms you need to know:
- FERPA: Family Educational Rights and Privacy Act
- PII: Personally identifiable information
U.S. Government and Military
All U.S. Government agencies and their business associates must follow FISMA, which follows NIST recommendations. Basically, these organizations must adhere to NIST recommendations as rules.
- Federal government agencies
- Businesses providing services on the behalf of or to any federal government agency (including YOU!)
Terms you need to know:
- FISMA: Federal Information Security Management Act
- NIST: National Institute of Standards and Technology
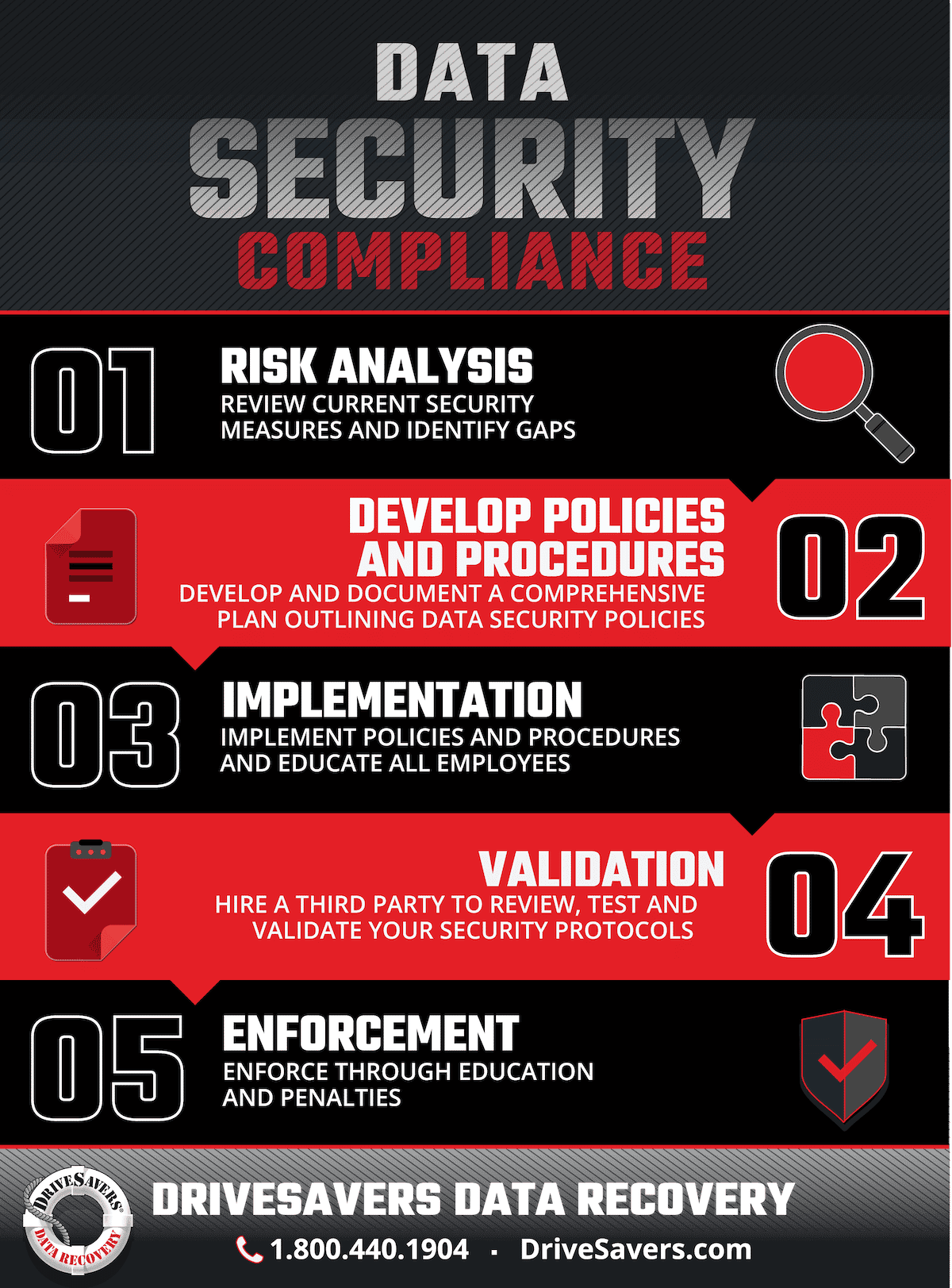
Five Steps to Compliance
One Path for All Industries
Despite different industries being required to follow differently named guidelines, there’s a pretty good overlap for those information security items that IT really needs to worry about.
Although there will be some personal information that may not fall under any compliance standards, from an IT perspective, it’s safe to assume that any and all customer, employee or other personal information needs to be protected from the breach, accidental exposure, or other cybersecurity transgressions.
In order to obtain and maintain compliance to any industry or government-mandated information security protocol, you must have documented and validated data security policies and procedures that are in use by your company.
The five steps you need to follow as IT regarding cybersecurity policies and procedures are fairly standard.
1. Risk Analysis
Risk analysis, sometimes also called gap analysis or security risk assessment, is the first step toward developing a data security policy. Security risk assessments should be conducted annually, biannually, or any time something changes, such as the purchase of new equipment or expansion of company services.
The purpose of risk analysis is to understand the existing system and identify gaps in policy and potential security risks. As explained by the SANS Institute, the process should work to answer the following questions:
- What needs to be protected?
- Who/What are the threats and vulnerabilities?
- What are the implications if they were damaged or lost?
- What is the value to the organization?
- What can be done to minimize exposure to the loss or damage?
Areas to review for proper security:
- Workstation and server configurations
- Physical security
- Network infrastructure administration
- System access controls
- Data classification and management
- Application development and maintenance
- Existing and potential threats
Methods of security to review:
- Access and authentication: access should be physically unavailable to anyone who is not authorized
- User account management
- Network security
- Monitoring
- Segregation of duties
- Physical security
- Employee background checks
- Confidentiality agreements
- Security training
This document from SANS Institute gives excellent instructions for conducting a thorough risk analysis for your company.
2. Development of Policies and Procedures
Based on the outcome of the risk analysis conducted, information security policies and procedures for safeguarding data must be updated or, if none currently exist, written from scratch.
Identify, develop and document:
- A comprehensive plan outlining data security and cybersecurity policies
- Individual staff responsibilities for maintaining data security
- Tools to be used to minimize data security risks, such as security cameras, firewalls, or security software
- Cybersecurity guidelines concerning the use of internet, intranet, and extranet systems
3. Implementation
Once your company’s information security policies and procedures have been identified, planned out and documented, they need to be implemented and followed.
- Purchase security software and other tools that have been identified as necessary
- Update existing software and operating systems that are out-of-date
- Conduct mandatory security training and awareness programs for all employees, and require signatures on mandatory reading materials
- Conduct background checks of all employees
- Vet third-party providers to be sure that they maintain and document compliant information security protocols identical to or more robust than those in place within your company
4. Validation
In order to prove that your company is compliant with industry regulations, you must have a third-party data security company validate your company’s security protocols, procedures and the implementation of those policies and procedures. This should be done annually or biannually.
This process can be pricey, time-consuming, and intrusive; however, this type of verification will both help your business to maintain data security and add value to your services for use by your customers.
A SOC 2 Type II security protocol can cover a large spectrum of industry-regulated data security requirements, including all of those discussed in this article: HIPAA, GLBA, SOX, FERPA, FISMA, and NIST.
5. Enforcement
Information security policies and procedures can be enforced through education and penalties.
You may have noticed that education falls under both implementation and enforcement. This is absolutely the most important part of your company’s information security and must be offered continuously. Mandatory data security training and awareness programs must be scheduled for employees to ensure sensitive and confidential data is protected. Be sure that anybody who might touch protected data is trained on current policies and risks, and kept current as policies are updated or new risks are identified.
For example, be sure that all relevant employees are aware of cybersecurity threats such as email phishing scams, how to identify them, what to do if somebody thinks they may be targeted, and what to do if they have become a victim, possibly exposing protected data. As new types of scams come into being, send company-wide emails detailing methods of identification and protection.
The second part of enforcement is eliminating the temptation to ignore data security protocols and encouraging compliance. This can be done by issuing penalties, financial or otherwise, for those who do not follow important procedures.
Industry compliance and overall data security will help maintain the safety of your organization’s data, and add a great selling point when pursuing clients.