By John Ahearne, Forensic Analyst When data is is needed for use as evidence, it…
The Wall Street Journal: Chip Hacking Might Help FBI Unlock iPhones
Originally published by The Wall Street Journal.
By Robert McMillan
Even if the Justice Department loses its legal showdown with Apple Inc. over access to a killer’s iPhone, the government might still be able to extract the data locked away inside it, computer-security experts say. But it would be risky, expensive and time-consuming.
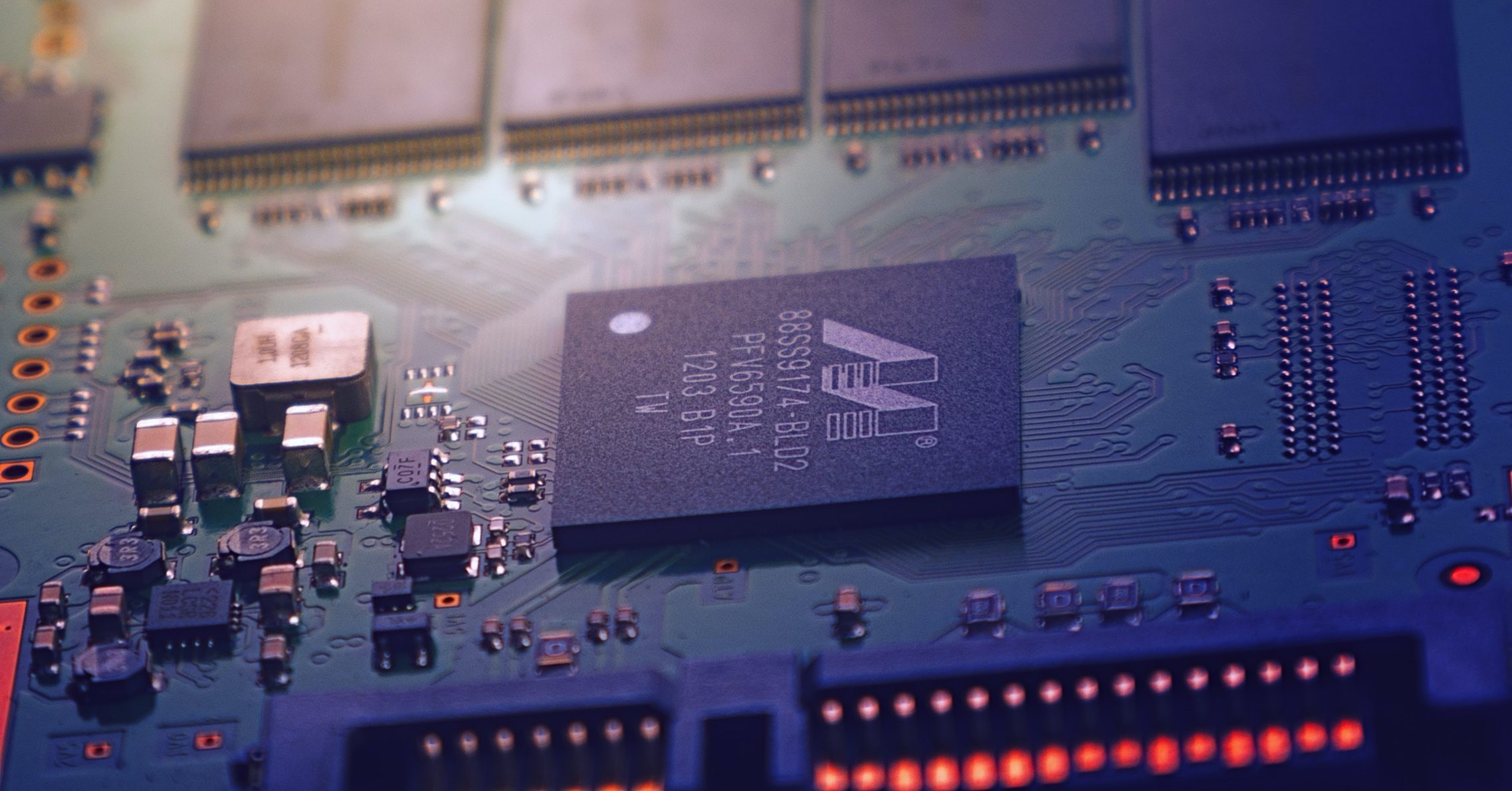
Those experts say officials could try to physically crack open the A6 microprocessor inside the phone of Syed Rizwan Farook, targeting the portion of the chip that holds the user ID, or UID, key. With the key, officials could move the iPhone’s scrambled data to another computer and quickly unlock it.
The most likely method to extract the key, the experts said, would be by using a focused ion beam–essentially a very precise atomic saw that can cut through the chip’s outer structures to expose the 1s and 0s stored in the chip.
The technique is theoretically possible, but would be “very difficult and expensive,” said Julia Elvidge, president of Chipworks Inc., an Ottawa company that specializes in opening and probing chips for patent violations.
Chipworks has done similar work in the past, using a focused ion beam to extract data from a damaged flight-control computer recovered from the cockpit of Swissair 111, which crashed near Peggys Cove, Canada, after catching fire over the Atlantic Ocean in 1998.
That chip was also encrypted. But reading data off a modern iPhone, with its much smaller circuitry, would be harder.
Ms. Elvidge and other security experts say that first the FBI would need to develop a technique to unlock the circuitry of an Apple chip–a kind of high-tech recipe that would require months of painstaking tests with other chips. Ms. Elvidge estimates that this work would cost between $500,000 and $1 million.
“A memory cell today is just a few dozen atoms wide,” said Karsten Nohl, chief scientist at Security Research Labs in Berlin. “If anything goes wrong in your setup….if there’s just the slightest vibration while you’re probing into your chip, it may be broken forever.”
Mr. Nohl has used a focused ion beam to extract data from smart-card chips. He says that cracking the iPhone would be much more difficult.
“It’s an option, but I think a very last resort because doing any kind of work on the chip itself risks breaking the chip for good,” he said.
Others think the technique is so unlikely to succeed that it isn’t worth trying. “We wouldn’t take such a project,” said Radu Trandafir, systems and software development lead at TechInsights Inc., which like Chipworks analyzes microprocessors. “It would have a very low probability of success.”
U.S. Rep. Darrell Issa (R., Calif.) Tuesday suggested another approach, asking Federal Bureau of Investigation Director James Comey during a hearing whether officials could make 10,000 copies of the chip inside Mr. Farook’s phone, and then try every conceivable password against them. Mr. Comey said he wasn’t familiar with the details of Mr. Issa’s approach, but was confident that the FBI had tried every possibility of accessing the phone before seeking a court order.
The bar to cracking an iPhone hasn’t always been so high. Until the iPhone 5, there were a variety of techniques that could unlock the phone’s data, through processes generally known as “jailbreaking” the phone, said Mike Cobb, a data-recovery expert at DriveSavers Inc.
His company has no way to get into Mr. Farook’s phone. But he said it is possible that someone has discovered a security hole in the iPhone design that would allow them to bypass the phone’s protections.
“Experience tells us that there probably are vulnerabilities,” he said. “They’re probably much harder to find and more difficult to exploit. They’re probably there.”
The Justice Department declined to comment for this article.
Write to Robert McMillan at [email protected]
Read more at: http://www.wsj.com/articles/chip-hacking-might-help-fbi-unlock-iphones-1457050959




