Symptoms of Ransomware Infection

By Mike Cobb, Director of Engineering
Ransomware is a quickly growing problem.
There were nearly 2,500 cases of ransomware reported to the FBI’s Internet Crime Complaint Center (IC3) in 2015 alone, and victims paid over 1.6 million dollars to unlock their data. 2016 is shaping up to show even larger numbers.
There are two types of ransomware: lockscreen and encryption.
Lockscreen ransomware provides a splash screen upon startup which prevents access to the computer. This splash screen provides instructions on how to pay a ransom to unlock the computer and access its contents.
Encryption ransomware encrypts the individual files on a computer. The user can browse folders on the computer, use a web browser and even create new files, but cannot access existing files. There is sometimes a splash screen to alert and instruct the user, but not always. Instead of an obvious splash screen, the user often must identify and open instruction files left by the hacker.
Are you having trouble accessing files on your computer? It’s not always obvious when ransomware is the problem. Here are some things to look for.
Files That Don’t Open
You are unable to access any of the files you try to open. You receive error messages, such as:
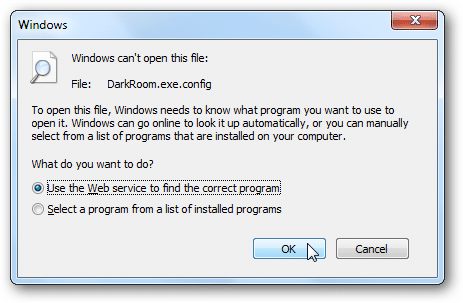
Windows
“Windows can’t open this file… To open this file, Windows needs to know what program you want to use to open it. Windows can go online to look it up automatically, or you can manually select from a list of programs that are installed on your computer.”
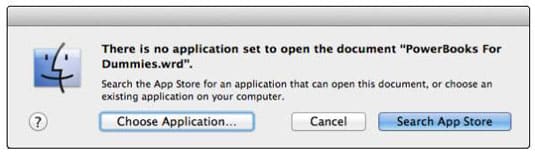
Mac
“There is no application set to open the document… Search the App Store for an application that can open this document, or choose an existing application on your computer.”
Odd or Missing File Extensions
Those letters after the dot at the end of a file name are the file extension. They let your computer know what type of file it needs to read. Common file extensions include .doc, .exe, .pdf and .jpeg.
Files encrypted by ransomware often have extensions that end with .crypted, .cryptor or something similar. Many times, these files are missing file extensions altogether. In all of these instances, the Finder will display a blank icon for the file type.
Instruction Files
The purpose of ransomware is for a hacker to hold your data for ransom. The goal is to get you to pay a ransom in exchange for a decryption key that will make your data available to you again. If your computer has been infected with ransomware, the hacker responsible will have left instructions for you.
Look for .txt or .html files that begin with an underscore (_) followed by clear language in all caps, such as “_OPEN ME”, “_DECRYPT YOUR FILES” or “_YOUR FILES HAVE BEEN ENCRYPTED.” There will be at least one instruction file located in every folder that contains data that has been encrypted by the ransomware. Remember—the hacker wants you to read these files, so they should be somewhat easy for you to find.
Note: Do not open these files unless you intend to follow through with a ransom payment.
Still Not Sure?
If you are still unsure whether or not you may be infected, a professional ransomware data recovery company, such as DriveSavers, can quickly determine the cause of your data loss and what the next steps are that should be taken.


