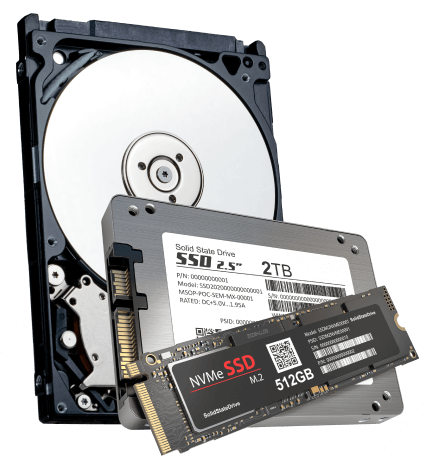
External and Internal Hard Drive Recovery Services
DriveSavers has established itself as a global frontrunner in hard drive data recovery services. Both individual users and enterprises trust DriveSavers to recover lost data from inaccessible internal and external hard drives, whether for Mac or PC.
The DriveSavers expert engineers consistently recover lost data from hard disk drives even when others have declared the data irretrievable — and we do it quickly.
Always avoid off-the-shelf data recovery software or tools. Such approaches could further damage the device and potentially make data unrecoverable.
DriveSavers engineers have an outstanding track record of retrieving misplaced or deleted files, including photographs. We pride ourselves on cutting-edge proprietary methods paired with straightforward solutions. Tap into our vast experience retrieving lost data from all data storage devices.
Whether you have a non-responsive hard drive, a compromised server, or a malfunctioning device, DriveSavers data recovery engineers excel at addressing these concerns and ensuring that you or your business don’t face data loss.
Hundreds of Thousands of Customers Trust DriveSavers
Companies Worldwide Trust DriveSavers
DriveSavers supports over 20,000 data recovery business partners worldwide. Your business could be one of them! Some of our satisfied customers include companies such as Coca Cola, Facebook, Google, AT&T, Sony, NASA, and many others.
We Can Save It!®
Each data loss situation is unique. The improper use of data recovery software could put your data at risk. DriveSavers has developed proprietary tools and data recovery techniques that allow us to deliver custom recovery solutions for every data loss scenario, including:
Logical Problems
- Firmware corruption
- File system corruption
- Lost passwords
- Deletions
- Partial overwriting
- Ransomware encryption
Physical Damage
- Dropped or crushed
- Liquid damage
- Contaminated
- Head crash
- Actuator failure
- Manufacturer defect
Natural Disasters
- Fire
- Flood
- Hurricane
- Tornado
- Earthquake
- Power spikes
Fast, Reliable, Secure
DriveSavers provides a comprehensive range of advantages in data recovery.
24—48 Hours
Industry-leading Standard turnaround time of 24 to 48 hours.
Diverse Service Options
A diverse range of service options to cater to every data recovery need.
Call 24/7
Direct phone support with expert Data Recovery Advisors, available 24/7.
Transparent Pricing
The first quote remains, ensuring no unexpected costs or hidden fees for services or parts.
Certified Secure
Stringent security certifications as mandated by the corporate clients, healthcare service providers, government agencies and individuals we serve.
“Always avoid off-the-shelf data recovery software or tools. Such approaches could further damage the device and potentially make data unrecoverable.”

Mike Cobb
Director of Engineering
DriveSavers Data Recovery
Manufacturer Approved
All leading storage media manufacturers authorize DriveSavers to open sealed storage device mechanisms without voiding the original warranty. Our data recovery allows you to receive an in-warranty device replacement from the manufacturer.
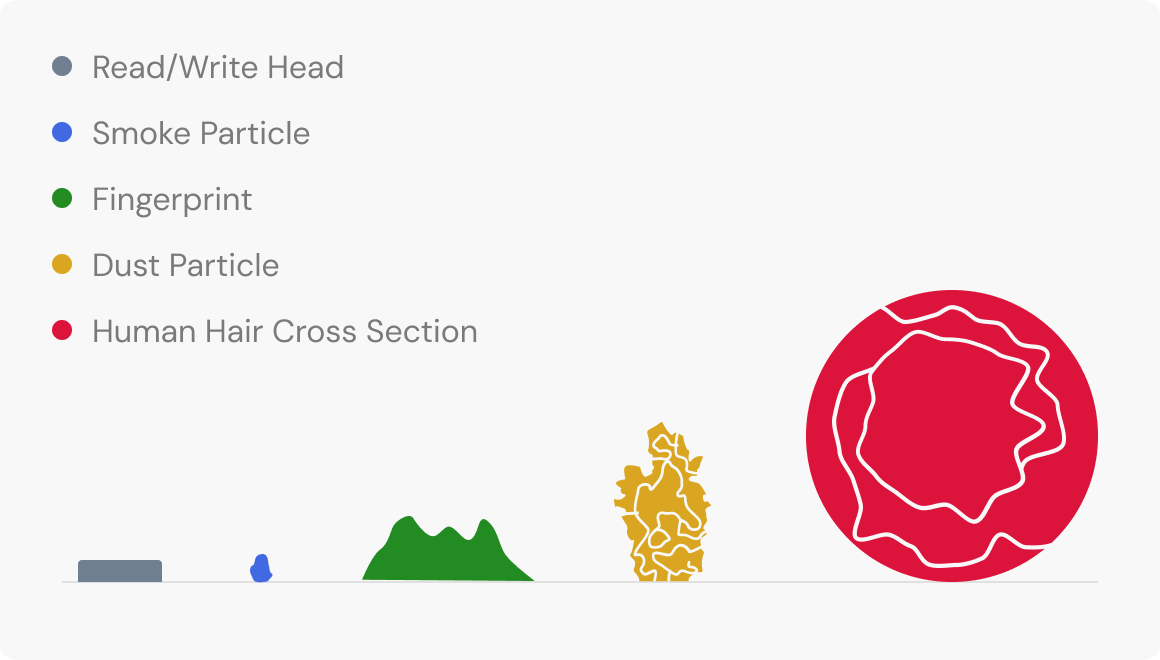
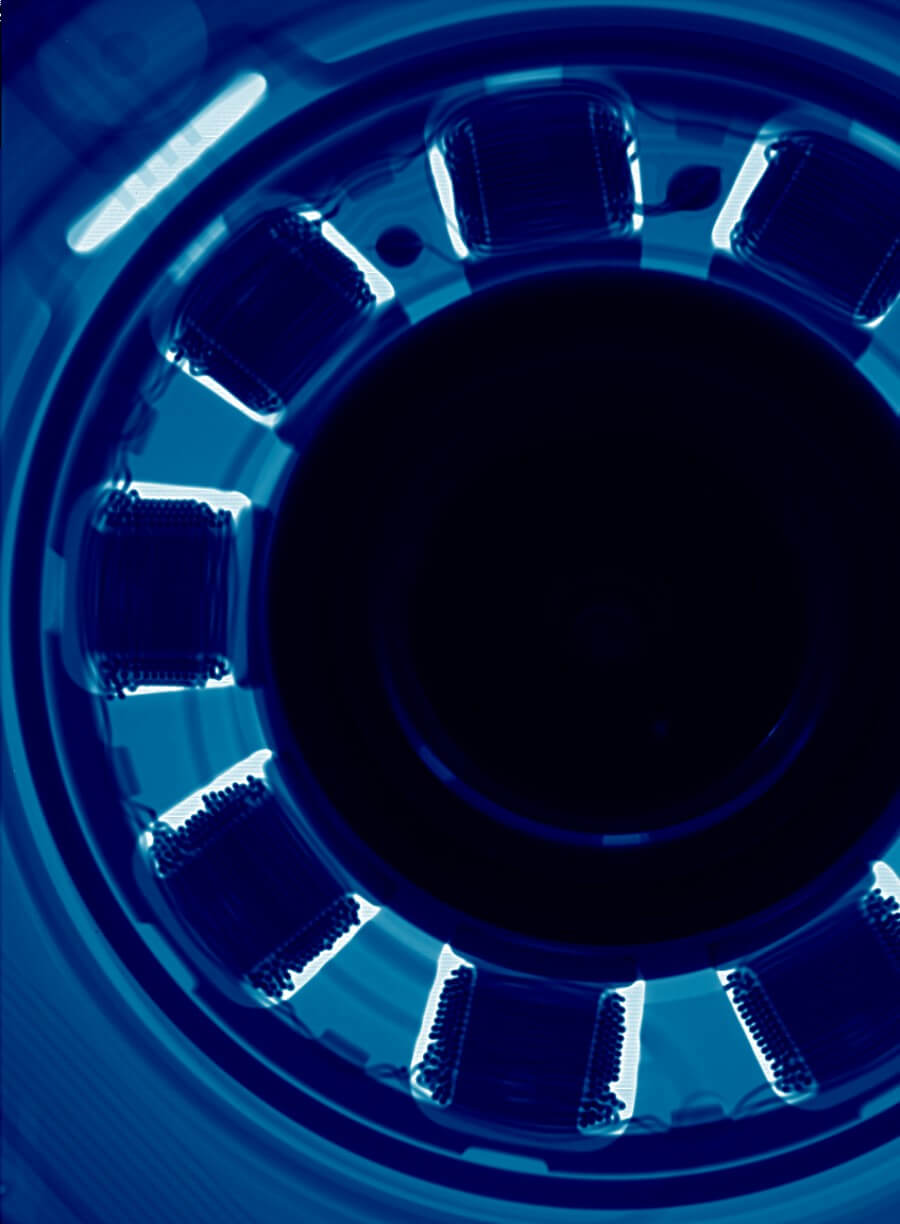
Certified ISO Cleanroom Maximizes Recovery Results
DriveSavers operates the industry’s largest state-of-the-art Certified ISO Cleanroom environment. To ensure the best possible outcomes in data recovery, all hard disk drive physical recovery operations take place in the DriveSavers state-of-the-art Cleanroom setting — the industry’s pinnacle of controlled environments.
The Certified ISO Class 5 Cleanroom adheres to the guidelines established by top-tier hard drive and data storage manufacturers. This is where DriveSavers engineers conduct a detailed examination of malfunctioning HDDs, assess them for physical defects, and carry out precise component-level repairs. Our recovery methods won’t invalidate the original hard drive warranty.
This image details the importance of opening a hard disk drive in an ISO-certified cleanroom. Tiny airborne particles can accumulate on the open hard disk drive platters, causing read-write heads to malfunction and damage the platter surface during the recovery process. Learn more.
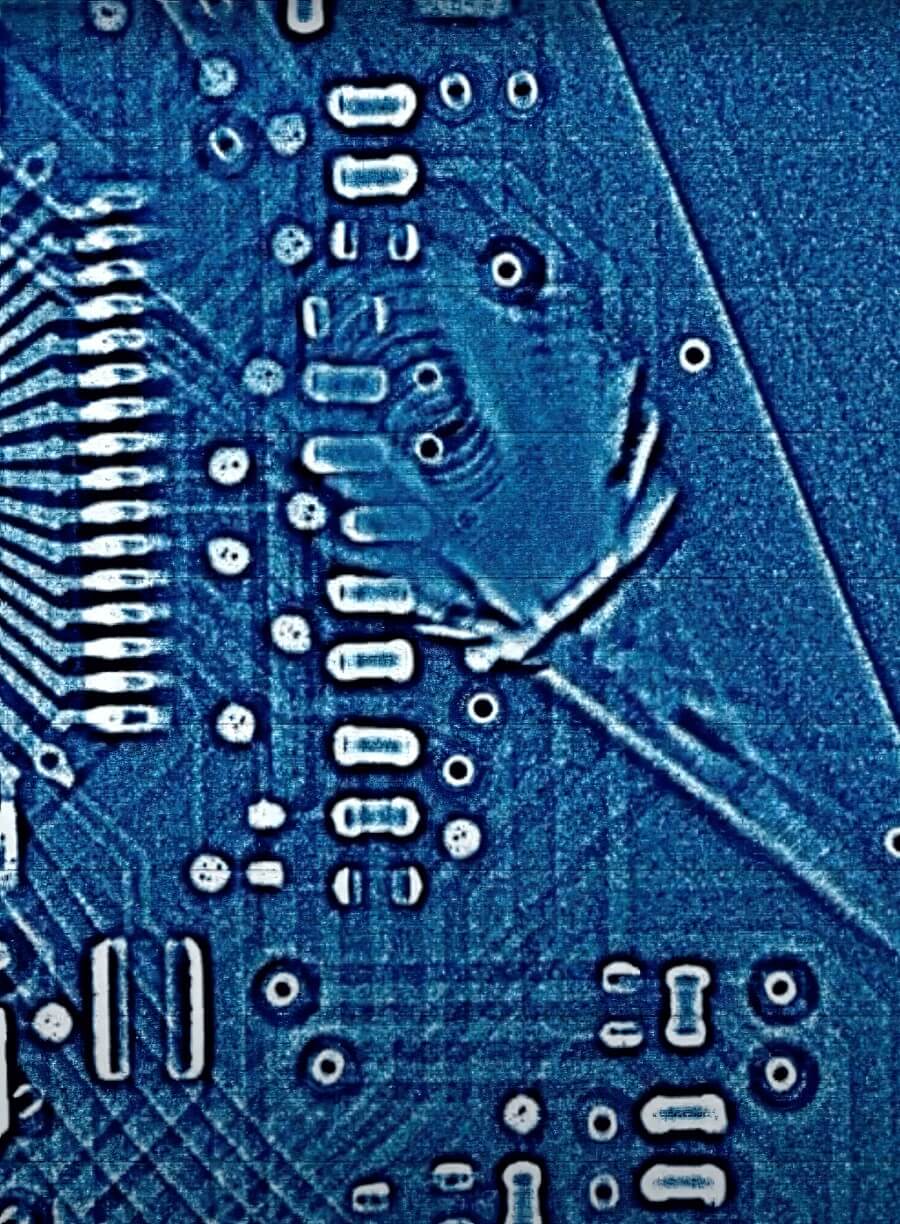

X-Ray Technology
DriveSavers utilizes X-ray technology for precise diagnostics, identifying irregularities and critical damage in storage media without risking device integrity. Using X-ray technology expands our data recovery capabilities, confirms suspected component failure, and validates proficiency of ball grid array (BGA) rework. No other data recovery service has this advanced technology in its lab.
Data Security
During Data Recovery
In the virtual world of the web, other data recovery companies may claim to provide the same levels of experience, service, and security as DriveSavers. But, can they really support what they say? DriveSavers provides proof.

Encryption Technology Specialists
DriveSavers data recovery engineers are well-versed in encryption technologies and the nuances required to recover data from failed hard drives of all kinds. Trained in leading encryption software, we are adept at safely retrieving both file and disk-level encrypted data. Whether it’s encrypted hardware, software, email, network storage, web content, or backup devices, rest assured that the original encryption standards will be maintained throughout the recovery process.
DriveSavers not only offers data recovery services, but we also understand the importance of tailored security protocols. We can adapt our services to meet your specific needs, providing you with a sense of security and reassurance.
Full Decryption
With your provided encryption keys, our engineers can recover and decrypt encrypted data, verifying its integrity. We can then return the data to you in either an encrypted or fully decrypted format, based on your preference.
Image-Only
With our Image-Only service, the data is retrieved as an exact image of the device to be re-integrated into your system while maintaining the original encryption settings. You’ll be responsible for decrypting the data once it’s returned.
Additional Security
Once the recovery is completed, we can securely and properly recycle the old storage device at no additional cost. Our NSA and DOD-approved degausser will destroy residual data on the old source drive permanently.

Call DriveSavers Day or Night
We will email a free shipping label and then call with the results of the evaluation and the cost to recover the data. If the data is not recoverable or you choose to decline the recovery, your cost is zero dollars.