Recycler ou réutiliser ?
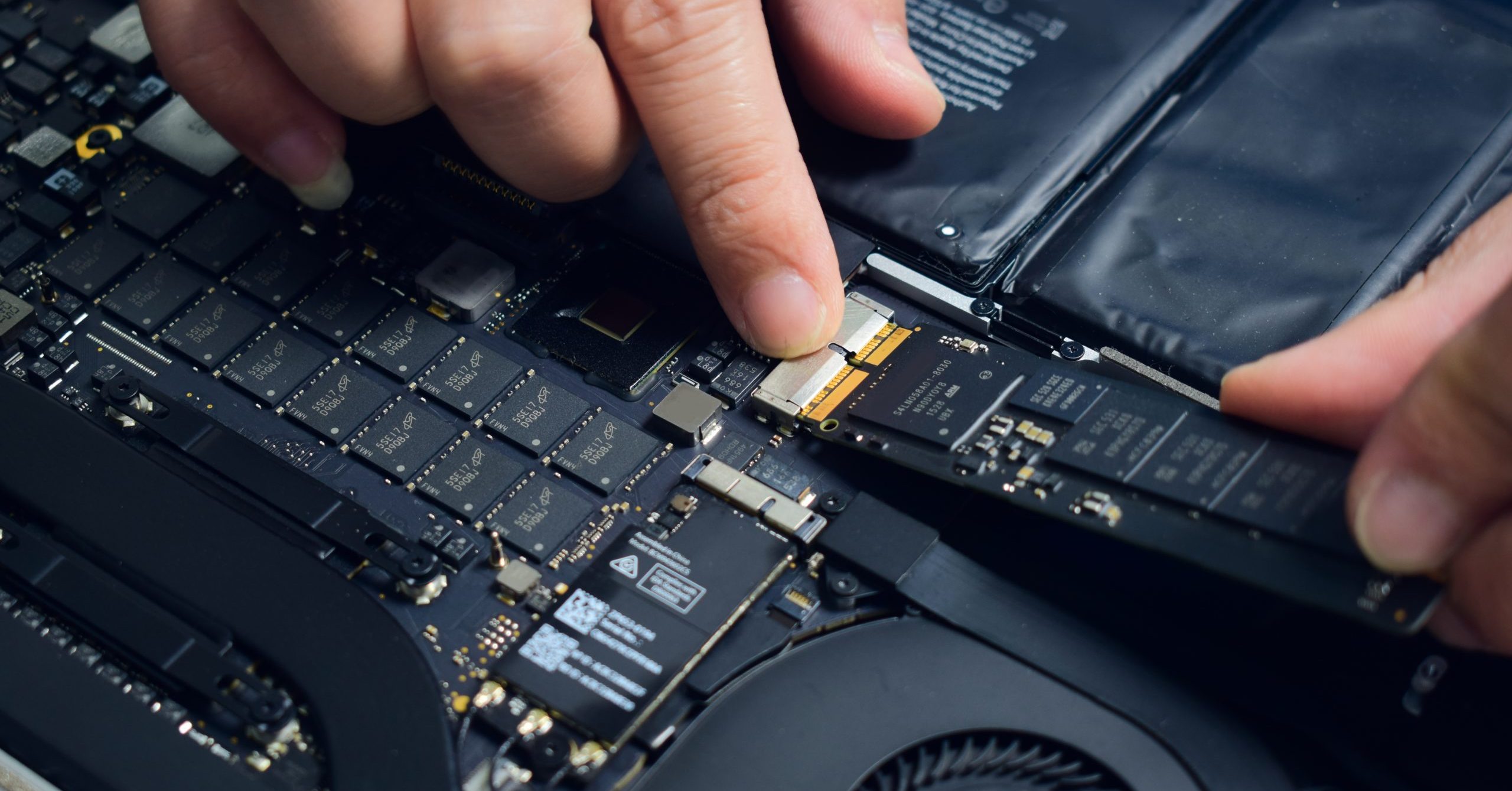
After a hard drive is recovered by DriveSavers, our standard practice is to return the equipment to the user. We don’t repair the drives so if they are not working when they come to the lab, they leave in the same condition. When a customer doesn’t want their broken equipment…