Why Ransomware Demands Are Increasing as Fewer Companies Pay
Ransomware demands surged 47% last year. And yet, a record number of organizations refused to pay them. You’d think those two trends would push costs down. They haven’t.
Understanding why matters a lot if your Incident Response plan currently starts and ends with backups.
Coalition’s 2026 Cyber Claims Report pulls from real claims data across more than 100,000 policyholders. It found that within that community, initial ransom demands averaged over $1 million in 2025, while 86% of targeted businesses refused to pay. That’s genuinely good news. Better backups, tested incident response plans, and skilled negotiators have given organisations leverage they didn’t have five years ago.
But ransomware incidents still rank as the most expensive type of cyber claim for Coalition insureds, averaging $302,000 per incident for the most common attack variant. Refusing to pay doesn’t mean walking away clean. It just means the costs are showing up somewhere else.
The old ransomware playbook was straightforward. Attackers lock your files, you restore from backup, you decline to pay, you move on. That still happens. But it’s no longer the main event.
In 2025, 70% of ransomware claims in Coalition’s data involved both encryption and data theft. The industry calls this dual extortion. Attackers don’t just lock your data. They take it first, and then they threaten to release it.
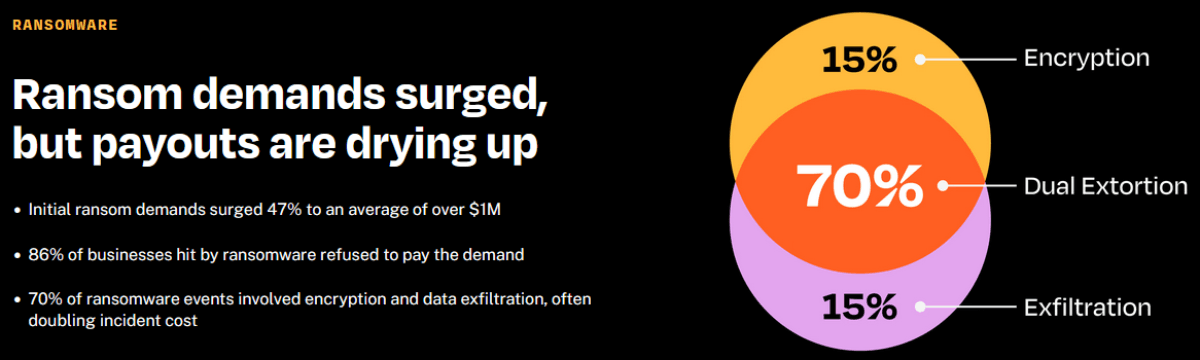
Allianz Commercial saw a similar shift in its claims data. In the first half of 2025, 40% of the value of large cyber claims involved data exfiltration, up from 25% for all of 2024. Those incidents cost more than twice as much as cases without data theft.
That gap makes sense when you think about what’s actually involved. Encrypted data is a recovery problem. Stolen data is a legal problem, a regulatory problem, and a reputational problem, one that can mean breach notifications, regulatory investigations, and litigation that drags on well after your systems are back up.
Good backups are still the foundation. If your systems can be restored cleanly, you’ve removed the attacker’s most immediate leverage, which is why the non-payment rate is at a record high.
The catch is that sophisticated ransomware actors know this. A common pattern is that they don’t just encrypt production systems and disappear. When possible, they spend time in the environment, mapping out how backups run and where they’re stored, and analyzing which critical data sets the organization can’t function without. Then, before triggering encryption, they go after the backups, encrypting or deleting them specifically to eliminate the easy recovery path. That’s the moment a ransomware incident becomes a business continuity crisis and a security problem.
And even if backups survive intact, they can’t undo exfiltration. Once data has left the environment, it’s out. The operational downtime ends when systems are restored. The exposure doesn’t.
In DriveSavers Data Recovery’s experience across thousands of recoveries, enterprise data recovery tends to come up in three situations that don’t get enough attention in most ransomware planning conversations.
DriveSavers works with organisations in all three of these situations, recovering inaccessible critical data when backups are gone, incomplete, or when decryption didn’t finish the job.
While 86% of businesses are now able to refuse ransom payments, the critical question remains: is your organization truly prepared to resist, or are you simply hoping for the best?
At minimum, that means three things:
1
Tested, off-site backups that are isolated from the production environment and verified regularly, not just assumed to be working.
2
An incident response plan that addresses dual extortion, not just encryption, with legal and communications protocols ready for data exposure scenarios.
3
A clear picture of your data recovery options when backups are partial, outdated, or gone.
Ransomware tactics will keep evolving. The window between initial access and data exfiltration is getting shorter. The organisations that come out of these incidents intact are the ones that treated recovery as a capability they built in advance, not something they figured out under pressure.
If you’re thinking through your ransomware response plan and want to understand where professional data recovery services fit, contact DriveSavers at +1 (437) 266-8341.
Sources
Coalition 2026 Cyber Claims Report: https://www.coalitioninc.com/claims-report/2026
Allianz Commercial Cyber Risk Trends 2025: https://commercial.allianz.com/news-and-insights/news/cyber-risk-trends-2025.html